Networking & Cloud Computing
epub |eng | 2019-06-24 | Author:Peter Yaworski [Peter Yaworski]
( Category:
Testing
June 23,2019 )
epub |eng | 2018-12-20 | Author:Marius Bancila & Richard Grimes [Marius Bancila]
( Category:
Internet, Groupware, & Telecommunications
June 19,2019 )
epub |eng | 2014-05-24 | Author:Mikolaj Jan Piskorski [Mikolaj Jan Piskorski]
( Category:
Marketing
June 16,2019 )
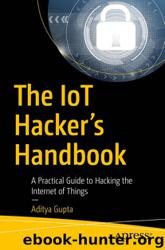
epub |eng | 2017-11-28 | Author:Aditya Gupta & Aaron Guzman [Aditya Gupta]
( Category:
Microprocessors & System Design
June 14,2019 )
epub |eng | | Author:Dhruv Shah
Similarly, you will need to include all the API keys here in recon-ng if you want to gather information from these sources. In the next recipe, we will learn how ...
( Category:
Network Security
June 10,2019 )
epub |eng | 2017-09-28 | Author:Rafay Baloch [Rafay Baloch]
( Category:
Hacking
June 10,2019 )
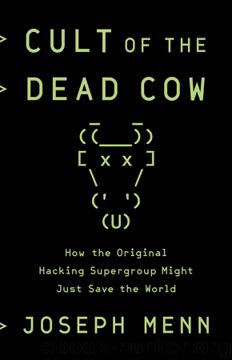
epub |eng | 2019-04-05 | Author:Menn, Joseph;
Laird also inspired what many independent security experts consider the best model for researching and exposing government use of the internet for repression: the Citizen Lab, at the University of ...
( Category:
Viruses
June 9,2019 )
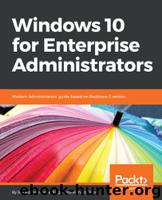
epub |eng | 2017-09-10 | Author:Richard Diver & Manuel Singer & Jeff Stokes [Richard Diver]
( Category:
Windows Administration
June 9,2019 )
epub |eng | 2017-11-16 | Author:Don Jones & Jeffery Hicks [Don Jones and Jeffery Hicks]
( Category:
Windows Administration
June 8,2019 )
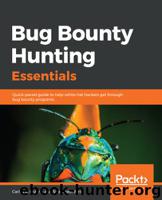
epub |eng | 2018-11-29 | Author:Shahmeer Amir & Carlos A. Lozano [Shahmeer Amir]
( Category:
Privacy & Online Safety
June 1,2019 )
epub |eng | 2019-05-25 | Author:Cornelia Davis [Cornelia Davis]
You’re now ready to launch the Connections service with the following command: kubectl apply -f cookbook-deployment-connections.yaml You can see the same configurations for the Posts service, which you can now ...
( Category:
Client-Server Systems
May 30,2019 )
epub |eng | | Author:Aditya Gupta
Let’s enter testing as the password here and press Enter. As soon as we press Enter, we can see that we have the breakpoint hit in the GDB session as ...
( Category:
Research
May 29,2019 )
epub |eng | 2019-05-03 | Author:Instafo & Derek Drake [Instafo & Drake, Derek]
( Category:
Privacy & Online Safety
May 29,2019 )
azw3 |eng | 2015-12-03 | Author:Steven M. Bellovin [Bellovin, Steven M.]
10.3 Sandboxes Sandboxing, sometimes known as jailing, is a class of techniques designed to limit the access rights—the effective target environment—of a program. The intent, of course, is to limit ...
( Category:
Hacking
May 28,2019 )
epub |eng | | Author:Michael McPhee
Tip If at any point you are unsure of your options, you can just type the help command. It will list all the available commands in that particular section. There ...
( Category:
Microprocessors & System Design
May 27,2019 )
Categories
Popular ebooks
The Mikado Method by Ola Ellnestam Daniel Brolund(25103)Kotlin in Action by Dmitry Jemerov(22332)
Grails in Action by Glen Smith Peter Ledbrook(18458)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15764)
Configuring Windows Server Hybrid Advanced Services Exam Ref AZ-801 by Chris Gill(7541)
Azure Containers Explained by Wesley Haakman & Richard Hooper(7525)
Running Windows Containers on AWS by Marcio Morales(7082)
Microsoft 365 Identity and Services Exam Guide MS-100 by Aaron Guilmette(5459)
Microsoft Cybersecurity Architect Exam Ref SC-100 by Dwayne Natwick(5304)
Ember.js in Action by Joachim Haagen Skeie(5249)
Combating Crime on the Dark Web by Nearchos Nearchou(5061)
The Ruby Workshop by Akshat Paul Peter Philips Dániel Szabó and Cheyne Wallace(4735)
Management Strategies for the Cloud Revolution: How Cloud Computing Is Transforming Business and Why You Can't Afford to Be Left Behind by Charles Babcock(4583)
The Age of Surveillance Capitalism by Shoshana Zuboff(4316)
Python for Security and Networking - Third Edition by José Manuel Ortega(4312)
Learn Windows PowerShell in a Month of Lunches by Don Jones(4307)
Learn Wireshark by Lisa Bock(4204)
The Ultimate Docker Container Book by Schenker Gabriel N.;(3949)
DevSecOps in Practice with VMware Tanzu by Parth Pandit & Robert Hardt(3643)
Windows Ransomware Detection and Protection by Marius Sandbu(3616)